Benefits
Experience the power of cutting-edge offensive security tools.
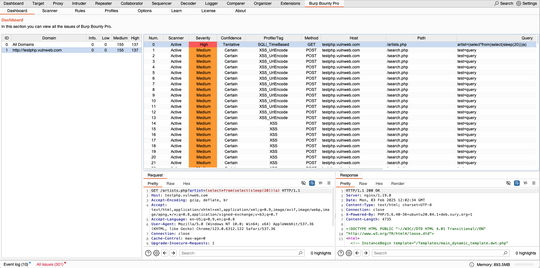
Pro Results
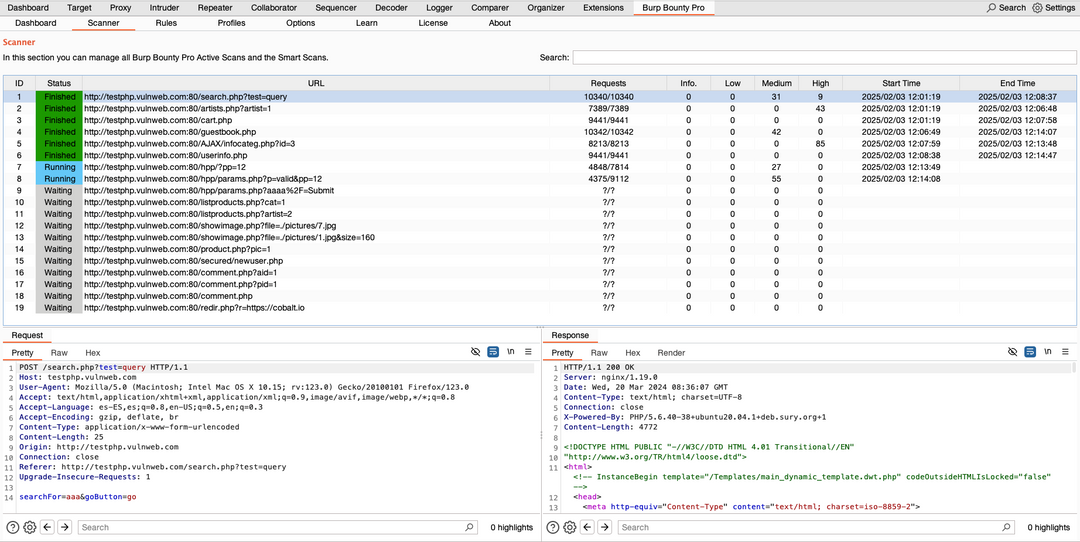
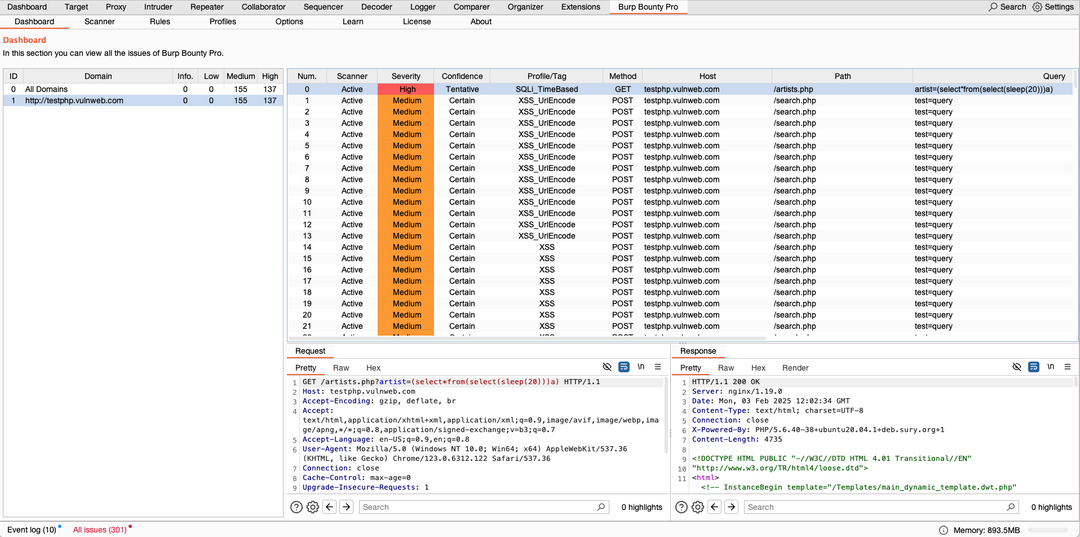
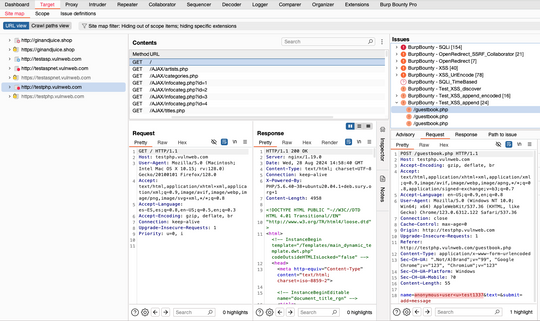
- One-Click Usage
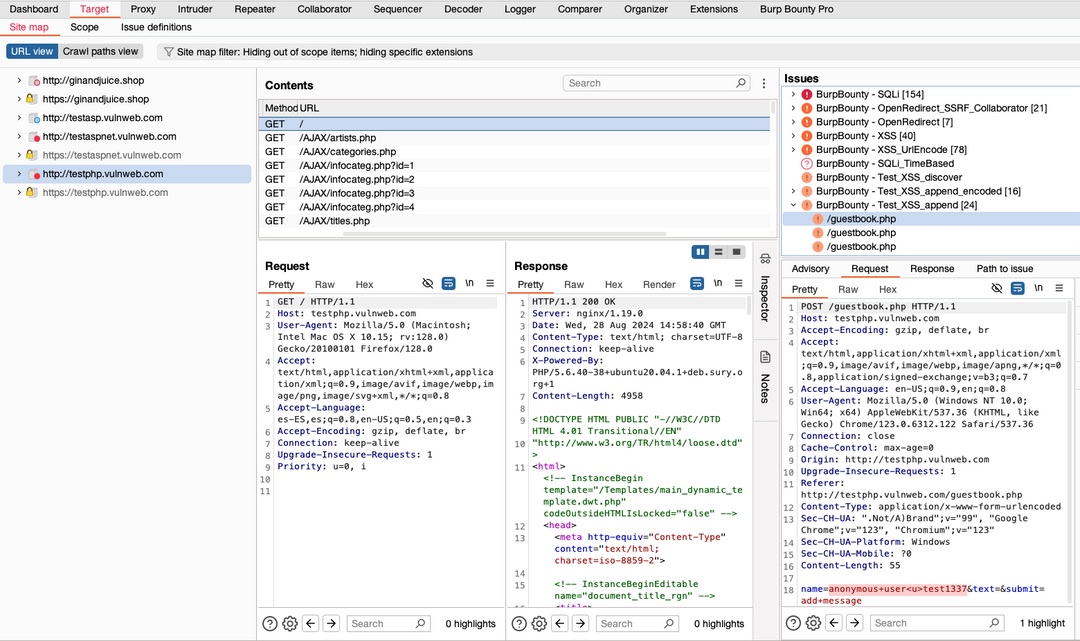
Launch scans instantly from Burp Suite Pro, saving you precious time. - Authenticated Coverage
Maintain session states to uncover deeper threats like broken access controls and logic flaws. - Depth & Power
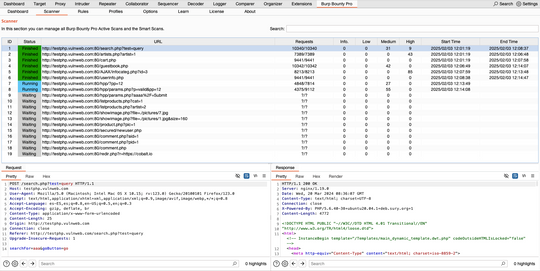
Multiple scanning modes and insertion points for comprehensive coverage. - Superior Efficiency
Experience rapid, accurate scans that free you to focus on critical analysis.
FAQs
They’re Burp Suite Pro extensions, so you’ll need Burp Suite Pro to use them.
Each license is user-based. With one license you have three device activations.
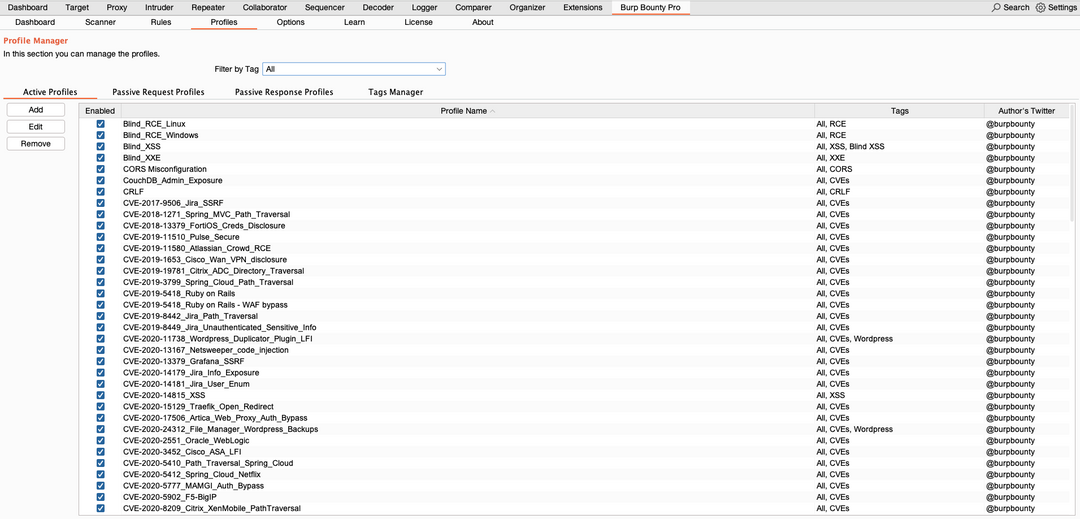
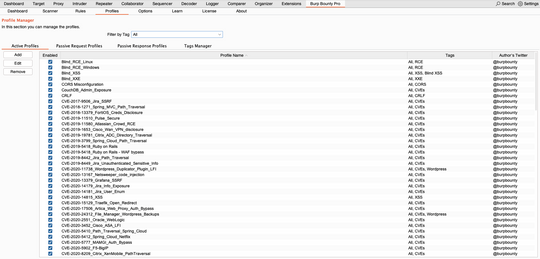
Burp Bounty Pro ships with ready-to-use profiles, but you can easily customize them for unique scenarios.
All scanners can produce false positives, but our optimized profiles help keep them to a minimum.
Visit our Documentation page for guides, best practices, and troubleshooting tips.
Or on our youtube channel:
And the twitter channel:
Verify your license key and ensure you’re running the latest version of Burp Suite Pro.
Ready to secure every hidden corner?
Get Burp Bounty Pro Now or Try it for Free and experience a smarter, faster way to protect your web applications—even behind login walls.